(5 min read)
Are you too small to be a target?
Most small and mid-sized businesses carry the same quiet assumption...
We’re not that interesting, we’re not that big AND we’ll be fine. And these beliefs are exactly what is making you attractive to potential hackers.
Hackers are not sitting around waiting for a household name. They are running volume. Automated scans, phishing campaigns, credential stuffing. You just need to be easier than the next business.
This is often the case for SME’s...

Not because they don’t care, but because they’re busy. You’ve got clients to serve, cash flow to manage, people to look after. Security ends up sitting somewhere between “important” and “later.” Attackers count on these gaps.
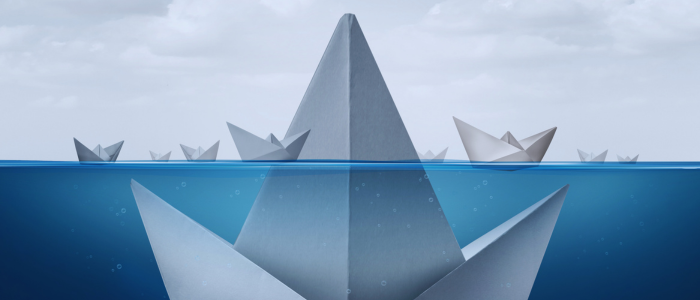
You’re not the target. You’re the entry point.
Here’s something most people miss. A lot of SMEs aren’t attacked for their own data. They’re attacked because of who they’re connected to. You’re a supplier, a partner, a stepping stone to something or someone more “worthy” in a hacker's world.

Recent incidents in engineering and manufacturing show this clearly. Smaller firms are being used as a way into larger organisations. One compromised inbox, one reused password and suddenly, someone else’s network is open.
You don’t need to be valuable. You just need to be connected.
And knowing this, changes the risk significantly!
The real damage isn’t technical
When people think about cyber-attacks, they picture systems going down. That’s part of it, but it’s rarely the part that hurts most. The real damage shows up in quieter ways, such as:
A client pauses a contract.
A partner asks more questions than usual.
A prospect goes cold after due diligence.
Larger organisations can absorb these kinds of damages. They have brand, PR teams, legal buffers. However, most SME's don’t.
If a customer starts to doubt how you handle their data, you don’t just lose one deal. You lose future ones you never even hear about. This is the part that nobody puts in the incident report.
“We have IT for that” is not a strategy
A lot of businesses feel covered because they’ve outsourced IT or installed security tools. It is certainly useful, but not always enough.
The Information Commissioner's Office (ICO) continues to highlight the same root cause in breaches. Not sophisticated attacks, but rather basic gaps in “organisational measures.”
When people do not know what to look out for nor understand and adapt behavioural patterns - that is when...
Someone clicks.
Someone shares access.
Someone does not report something because they aren't sure if it matters.
This does not happen when technology fails, but rather the systems around it fails.
The cheapest control you’re not using properly
If you ask most SME leaders where they’d invest in security, they’ll point to software such as firewalls, detection tools, monitoring etc.

These ARE all important, but none of them help when someone types their password into a fake login page at 4:52pm on a Friday.
Or more recent attacks where hackers are impersonating IT Helpdesk / IT support teams, requesting access to aid with support. You can read more about this here.
Your people are already your biggest attack surface, yet can also be your best line of defence.
But only if they’re prepared. Not with a once-a-year training module everyone clicks through while half-watching emails. That doesn’t stick.
People need short, regular prompts and real examples. Situations that look like their actual workday. The kind where they think, “oh, I’ve seen that.”
That’s how behaviour shifts. Not through information, but through repetition and relevance.
A better question to ask
Instead of asking the question, “Are we secure?” Ask something more uncomfortable; “If one of our team made a simple mistake tomorrow, how bad could it get?” Because that’s the scenario that plays out most often.

Start small but make it real. You don’t need a massive programme to move the needle.
Talk openly about mistakes.
Show what a phishing email actually looks like today.
Make it easy to report something without feeling stupid.
Repeat the important stuff more than once.
Make security a part of how you work, not something separate from it. Letting it become part of everyday activity is when it starts to stick.
If you take one thing from this, you are not too small to be overlooked when it comes to cyber security. What hackers are looking for are small, underprepared and connected enough.
The good news is that this is fixable, not by introducing more fear, but with better habits.
And that starts with your people – effective training is certainly one way.
This can be done as part of your IT policies and without a huge investment in time or cost, whilst giving your business more protection from attack.
In a previous blog we talk about learning how to manage security when you are time-poor and cash-poor.
Want to find out how effective, affordable training can change the behaviours of your staff? Contact us today at Cette adresse e-mail est protégée contre les robots spammeurs. Vous devez activer le JavaScript pour la visualiser..
Remember – your people are your first line of defence.
If you’d like to strengthen the human side of your cyber resilience, at work or beyond it, sign up for our newsletter for straightforward insights that actually stick.
Mark Brown is a behavioural science expert with significant experience in inspiring organisational and culture change that lasts. If you’d like to chat about using Psybersafe in your business to help to stay cyber secure, contact Mark today.
